DeM Banter: Spot on… we are trying to apply old Industrial Age Warfare paradigms and rules to a new Information Age Enemy–we are better than that. This enemy does not rely on the old style of C2–they are patient and will morph as only a “leaderless organization” can. Many experts feel we are on AQ 4.0 at this point…To yell WE WIN and leave the battlefield is not only juvenile–it is deadly.
Washington Post
August 6, 2013
Pg. 19
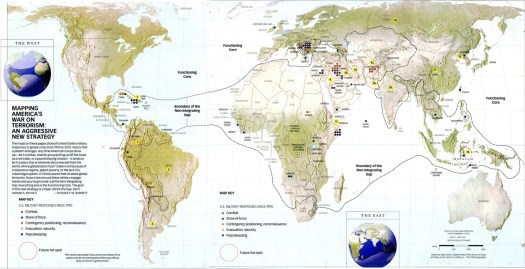
The new threat warnings of an al-Qaeda-driven plot in the Middle East and North Africa have reminded Americans that the terrorist threat persists even though Osama bin Laden is dead and the core of al-Qaeda is decimated. They are also a timely wake-up call to the broader terrorist threat now entrenched throughout an “arc of instability” – from South Asia to West Africa, where our diplomatic posts have been closed because of the reported threats – that we can’t ignore.
The inability to grasp the gathering threat from al-Qaeda prior to Sept. 11 was deemed a failure of imagination. Given the globalized nature of terrorism and the ability of transnational terrorist, militant and criminal groups to collaborate and morph, we are now at risk of failing to imagine how the terrorist threat may be changing – well beyond the exclusive al-Qaeda prism.
The U.S. government has been surprised by terrorist adaptations including al-Qaeda affiliates and fellow extremist group plots aimed at an airliner flying over Detroit; New York’s Times Square; and Mumbai, India , where an American helped planned the 2008 attacks. Even the fact that the Boston Marathon attackers gained ideological grounding from the violent extremism in the Caucasus seemed to have caught officials and the public off guard.
Though the al-Qaeda core has been decimated, its regional affiliates have adapted – embedding themselves in local insurgencies such as al-Shabab in Somalia; supporting operations between groups, such as al-Qaeda in the Islamic Maghreb and Boko Haram in Nigeria; and engaging in criminality, including smuggling, drug trafficking, bank robberies and kidnapping in the Maghreb, Iraq, Southeast and Central Asia.
Militant groups in this arc of instability exploit havens where weak or corrupt governments have neither the will nor the capacity to constrain their reach. Our recent fieldwork in South and Central Asia – including in Afghanistan and Pakistan – reveals a patchwork of violent extremist groups, fractured yet adapting to wage international plots after years of U.S. counterinsurgency operations. They are waiting for the withdrawal of U.S. troops to energize a narrative of defeat of the world’s remaining superpower – equating 2014 to the Soviet withdrawal from Afghanistan in 1989. Meanwhile, the Internet amplifies terrorist ideologies and messages for a global jihadi community.
Perhaps the most worrisome development is that the Levant is now at the center of this instability. As turmoil, violence and disillusionment grip the region from Tunis to Baghdad, al-Qaeda’s ideological adherents have more political and physical space in which to adapt.
In Syria, al-Qaeda has a new cause to galvanize foreign fighters and fuel its mythology in the region central to its strategy. Groups fighting under the al-Qaeda banner, such as Jabhat al-Nusra, are learning from past mistakes and establishing social services – baking bread and mending wounds – to win the hearts and minds of their constituency. This contrasts with the alienating brutality of Taliban rule and the horrific campaigns by al-Qaeda in Iraq.
Dangerously, the fighting has stirred the historic Sunni extremist funding networks – supported by states and donors from the Arabian Peninsula – with calls from Sunni clerics to send money and manpower to fight Syrian President Bashar al-Assad and the Shiite “devils.”
We therefore cannot assume that the terrorist threat to the United States will manifest itself as it has in the past. Identifying threatening groups or cells will be difficult – as seen in Benghazi. Distinguishing between terrorism, local militancy and criminality will grow more challenging – as seen in West Africa. Predicting which affiliates or groups present an imminent threat to the United States may become a nearly impossible task – as seen in Yemen.
Recognizing the adaptations matters now.
Leveraging regional alliances to constrict the reach of regional terror groups is essential. Law enforcement authorities need to aggressively pursue the terror-crime nexus. Our withdrawal from Afghanistan must be calibrated to account for the realities of emerging threats, not just the original threat that caused us to destroy the al-Qaeda haven. Ensuring that Syria does not become the locus for al-Qaeda’s rebirth should also be a principal policy goal, along with the fall of Assad.
The debate around the Authorization for Use of Military Force should address how we define the enemy and preserve the ability to fight whatever emerges from this cauldron of conflict. Just as President Obama was given the tools and strategies needed to fight al-Qaeda – and amplified many of them – his administration must continue to ensure that the country can adapt to looming threats.
Now is the time to shape a counterterrorism approach that is not simply reacting to battles of the past but preparing for the tide of threats that may reach our shores. The fight against the al-Qaeda core may be coming to an end, but we can’t blind ourselves to the terrorist adaptations already underway.
Juan Zarate is a former deputy national security adviser for combating terrorism and the author of the forthcoming “Treasury’s War: The Unleashing of a New Era of Financial Warfare.” Thomas Sanderson is the co-director of the Transnational Threats Project at the Center for Strategic and International Studies.